##Update:## Additional information about this campaign:
The following malicious pages are active at the time of writing:
s3-us-west-2.amazonaws.com/pop0402155/chrome/8222/index.html
https://d1fxjjqqqgobxf.cloudfront.net/
https://d1u0tb6g7laz1.cloudfront.net/
www.microsoft-security-fix-now.cf/call-microsoft-support-at-1-855-633-1666/
http://orthodoxyinnocuity.bid/139/0d1a07deab0631_b2fac41adda7f52486/
https://microsoft-alert-contact-help.cf/call-microsoft-support-at-1-800-876-0491/
https://d25nmjf4o2m1x1.cloudfront.net/
The following pages were contained in the emails themselves, and redirect to the malicious pages:
http://csasesores.com.ar/psychologically.php
http://vltammaro.com/mould.php
http://denver.boson.posiweb.net/userfiles/appointive.php
http://xujixmedia.com/graft.php
http://polinit.ru/modularization.php
http://smile-itconsult.com/school-intranet/upload/mod_photoalbum/501/file_attach/original/colonizes.php
http://pnpsteeltrading.com/apology.php
http://www.39hx.net/wp-content/marshaled.php
http://amicaminsurancegroup.net/resourcefulness.php
The following emails were received:
Very common browser locker/text support scam setup. The malicious pages in this campaign are not sophisticated. If the user has not clicked anywhere on the page, they can simply navigate away. If they have, the page will become full screen, and it will require the use of keyboard shortcuts to open a task manager and terminate the browser process.
The email, received July 26, 2017 was purporting to be a Facebook password reset link. The sender email was unrelated to the source IP of the message so it was redacted.
The header of the email shows a source IP address of 128.199.119.215. This address resolves to a Vietnamese domain that appears to be a restaurant website. Excuse my lack of Vietnamese language skill.
The link goes to a domain csasesores[.]com[.]ar/psychologically[.]php. The page is a simple javascript redirect that is obfuscated. The comment in the code below shows what is generated by the method:
This kicks of a chain of redirects, presumably for ad revenue generation (line wraps for readability):
http://fitness-4weiight-losess.world/?a=401336&c=cpcdiet&s=250717
http://tipforso.com/d/r6t0b27039?rtb=bbf5c3c30a4a6a7b1440169be16100c4.0&h=0.19&rtc=
45894_3ee488cf0a1ea2296c4bc36fbf092837_20d8d3b76a136b7cbd7084b33ac8d6fc1501110506.2487_205_02&subid=NDAxMzM2LU1qVXdOekUz
http://blobar.org/d/r6t0b27039?k=b70be0c41fa291af6fadfe5320455f86.1501109837.907.1&rtb=bbf5c3c30a4a6a7b1440169be16100c4.0&h=0.19&rtc=45894_3ee488cf0a1ea2296c4bc36fbf092837_
20d8d3b76a136b7cbd7084b33ac8d6fc1501110506.2487_
205_02&subid=NDAxMzM2LU1qVXdOekUz&r=http%3A%2F%2Fcsasesores.com.ar%2Fpsychologically.php&z=420
The final request is redirected back to the original domain, with a GET parameter that (I assume) triggers the final redirect to a variety of generic browser lock pages. In addition to the visual components, audio of a computer generated voice warns the user that their sensitive data is being transmitted to "hackers":
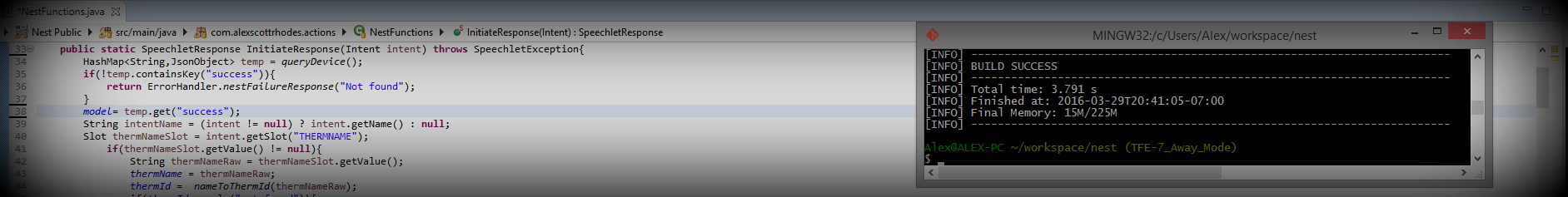
The following code is from one of the lockers. They appear well known, and have been previously submitted to VirusTotal and malware sharing sites. Some extraneous lines are omitted and the comments provide a summary of the functionality. The first image is the main "locking" component, an alert dialog that is created repeatedly:
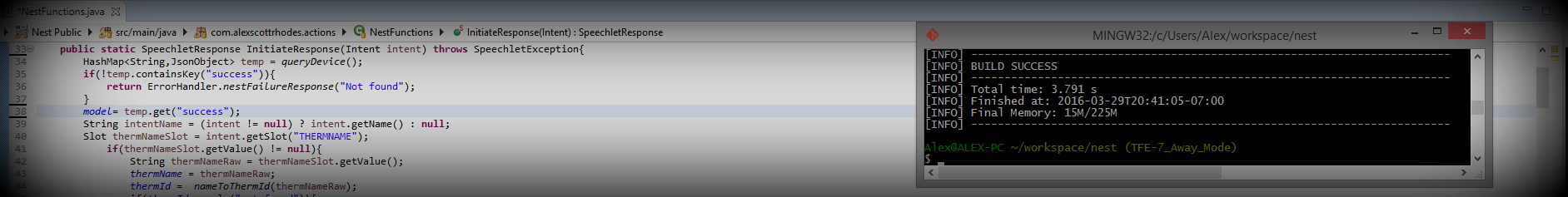
Interestingly, there is a google analytics object embedded in the pages. It can be seen in the last image. It is possible that this object could help to identify the author. The code contains an iframe that is programmatically directed to the following URL:
http://104.238.96.35/~error560x21/report.php
That IP is associated with the domain groovyshop.xyz. Directly accessing the domain resulted in a 404.
The pages are served by Amazon Web Services at the following URLs:
s3-us-west-2.amazonaws.com/pop0402155/chrome/8222/index.html
https://d1fxjjqqqgobxf.cloudfront.net/
https://d1u0tb6g7laz1.cloudfront.net/
One page was hosted at a different URL, hosted by GoDaddy, using a free domain name from Freenom, a company in the Netherlands:
www.microsoft-security-fix-now.cf/call-microsoft-support-at-1-855-633-1666/
The only trail (that my limited PI skills discovered) was the Google Analytics object seen above. The following WHOIS lookups on the associated domains described above may or may not be useful:
Virus Total reports for the various domains and IP addresses:
IP Report:
VirusTotal - csasesores.com.ar
These types of campaigns are exceedingly common. Non-savvy users may get roped into calling the fraudulent tech support numbers and end up falling victim to a typical support scam. No malware was obtained directly from these emails, but it is likely that anyone allowing remote access to a tech support scammer may fall victim to an infection.